08/05/2026 06:51am
EP.124 Advanced Security & Authentication for WebSocket (JWT, Token Strategy & Secure Handshake)
#JWT WebSocket
#Go
#WebSocket
#WebSocket Authentication
#WebSocket Security
When your WebSocket server starts handling a large number of users or is used for critical, sensitive data, such as:
- Chat & Collaboration Systems
- Financial / Trading Platforms
- IoT & Device Control
- Multiplayer Games
- Internal Enterprise Systems
The most important question is no longer: “How fast is it?” But instead:❗ “Is it secure enough for production?”
This article takes you deep into real-world WebSocket security, covering patterns and practices used in enterprise and large-scale production systems.
🎯 What You Will Learn
After reading this article, you will understand:
- How to implement proper WebSocket authentication
- How to use JWT and token strategies securely
- How to prevent WebSocket hijacking
- How to design a secure, production-ready handshake
- Why Authentication ≠ Authorization in real-time systems
🧠 Common Misconceptions About WebSocket Security
Many developers still believe:
❌ “WebSocket is already secure because it starts from HTTP”
❌ “Checking the user once during connection is enough”
❌ “Cookie-based authentication works just like normal web apps”
The Reality
- WebSocket is a long-lived connection
- One successful connection can stay alive for hours
- WebSocket does not enforce Same-Origin Policy like fetch/XHR
- If authentication fails at the handshake → the entire session is compromised
🔥 An incorrectly authenticated WebSocket is like leaving the door open all day
🔑 WebSocket Authentication The Right Way
❌ What You Should Never Do
- Send username/password via WebSocket messages
- Authenticate after the connection is established
- Trust client-side data
- Rely solely on cookies
✅ The Correct Approach
- Authenticate during the handshake
- Reject the connection immediately if authentication fails
- Use token-based authentication
🪪 JWT & Token Strategy for WebSocket
Recommended Flow (Best Practice)
- Client logs in via REST API
- Server returns a short-lived JWT
- Client uses the JWT when connecting to WebSocket
Passing the Token
Via Query String
wss://api.example.com/ws?token=JWT_TOKEN
Via Header
Authorization: Bearer <JWT>
✅ Header-based auth is preferred when supported by your Load Balancer / Ingress
⚠️ Query strings require caution due to logging and monitoring tools
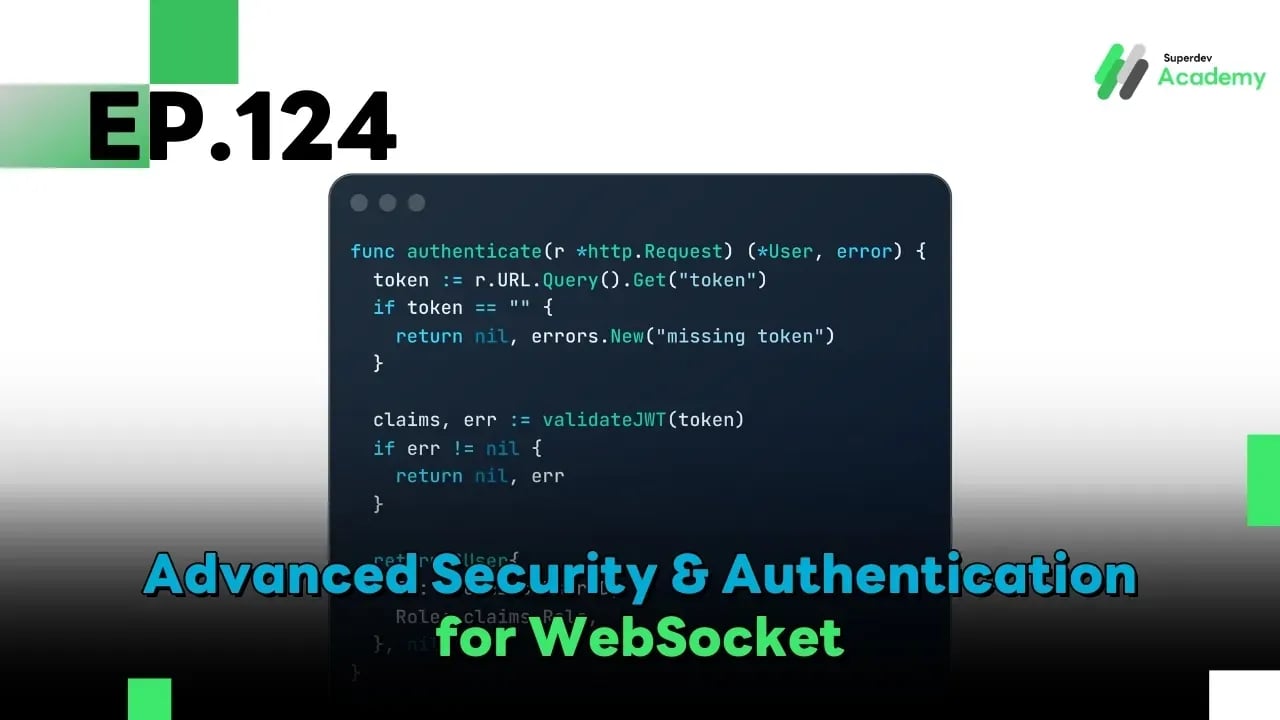
🧩 JWT Validation During Handshake (Go Example)
func authenticate(r *http.Request) (*User, error) {
token := r.URL.Query().Get("token")
if token == "" {
return nil, errors.New("missing token")
}
claims, err := validateJWT(token)
if err != nil {
return nil, err
}
return &User{
ID: claims.UserID,
Role: claims.Role,
}, nil
}
❗ If authentication fails → reject the connection immediately
Never open a WebSocket and validate later.
⏳ Token Expiration & Refresh Strategy
Real-World Problem
- WebSocket connections are long-lived
- JWTs should be short-lived
- Tokens can expire during an active session
Production-Proven Strategy
- Use short-lived JWTs
- Refresh tokens via REST API
- Send a
reauth_requiredevent through WebSocket - Gracefully disconnect if re-authentication fails
❌ Never solve this by issuing long-lived JWTs
🧨 What Is WebSocket Hijacking?
Common Attack Scenario
- Attacker injects malicious JavaScript
- Browser automatically sends cookies
- Attacker opens a WebSocket as the victim
- Server believes it’s a legitimate user
⚠️ WebSocket connections are not protected by Same-Origin Policy
🛡️ How to Prevent WebSocket Hijacking (Mandatory)
1. Always Validate the Origin
func checkOrigin(r *http.Request) bool {
origin := r.Header.Get("Origin")
return origin == "https://yourdomain.com"
}
❗ Never return true unconditionally in production.
2. Never Use Cookie-Only Authentication
- Cookies are sent automatically
- Vulnerable to CSRF and hijacking
✅ Use token-based authentication only
3. Bind Tokens to Context
Bind JWTs with additional context such as:
user_iddevice_idsession_idip(optional)
This helps prevent token replay attacks
🤝 Secure Handshake Design (Enterprise Grade)
A secure handshake should include:
- JWT validation
- Origin check
- Rate limiting per IP
- Permission check
- Rejection of unknown protocols
Recommended Flow
Client → Handshake
→ Validate JWT
→ Check Origin
→ Check Permission
→ Accept / Reject
🚨 Rate Limiting & Brute-force Protection
Threats to Defend Against
- Connection flooding
- Token brute-force attacks
- Reconnect spam
Production Solutions
- Limit connections per IP
- Redis-based rate limiter
- Exponential backoff on the client side
🔐 Authorization Inside WebSocket (Critical)
Authentication ≠ Authorization
Common Vulnerabilities
- User sending messages to admin-only rooms ❌
- User subscribing to restricted events ❌
Correct Approach
- Check role and permissions for every event
- Validate every message
- Never trust client-side event types
🧪 Production Security Checklist
✅ Use WSS:// only
✅ Validate JWT during handshake
✅ Check Origin
✅ Enforce token expiration
✅ Never send sensitive data in plain text
✅ Rate limit connections
✅ Log security events
✅ Monitor reconnect anomalies
🚀 Challenge: WebSocket Security Audit
Try auditing your own system:
- Remove cookie-based auth
- Enforce JWT validation at connect time
- Attempt connections from other domains
- Test expired tokens
- Flood reconnect attempts
If your system survives all of these → you’re approaching enterprise-grade WebSocket security 🔐
🔮 What’s Next EP.125 TLS / WSS & Certificate Management for WebSocket
In the next episode, we will dive into:
- HTTPS vs WSS
- TLS Handshake
- Certificate Rotation
- Let’s Encrypt & Production Setup
- Zero-downtime Certificate Renewal