08/05/2026 06:51am
Golang The Series EP.137: Enterprise WebSocket Security – Building an Unbreakable Fortress
#Golang
#WebSocket
#Go
#cybersecurity
#CSWSH
Welcome back, Gophers! Many developers believe that simply switching from ws:// to wss:// (TLS) is enough to secure their real-time systems. In reality, that’s just "locking the front gate." Enterprise-grade security requires a Defense in Depth strategy that spans the Application Layer, Infrastructure, and Resource Management.
Today, we are diving deep into the 5 Pillars of WebSocket Security to protect your system from attackers who are looking for any crack in your armor.
1. Authentication & Authorization: The Gatekeeper
Standard Browser APIs for WebSockets do not support custom HTTP Headers during the handshake (new WebSocket()). This means the usual Authorization: Bearer <token> approach won't work out of the box.
Recommended Strategies:
- Ticket-based Authentication (The Gold Standard): 1. The client requests a "One-time Ticket" via a secure REST API.
2. The server generates a short-lived ticket (e.g., valid for 30 seconds) and stores it in Redis.
3. The client passes this ticket via a Query String when opening the WebSocket.
4. The server validates the ticket and deletes it immediately (Delete on Read) to prevent Replay Attacks. - Periodic Re-authentication: For long-lived connections (hours or days), force the client to re-verify their identity (using a Refresh Token) through the existing WebSocket pipe. If they fail, terminate the connection instantly.
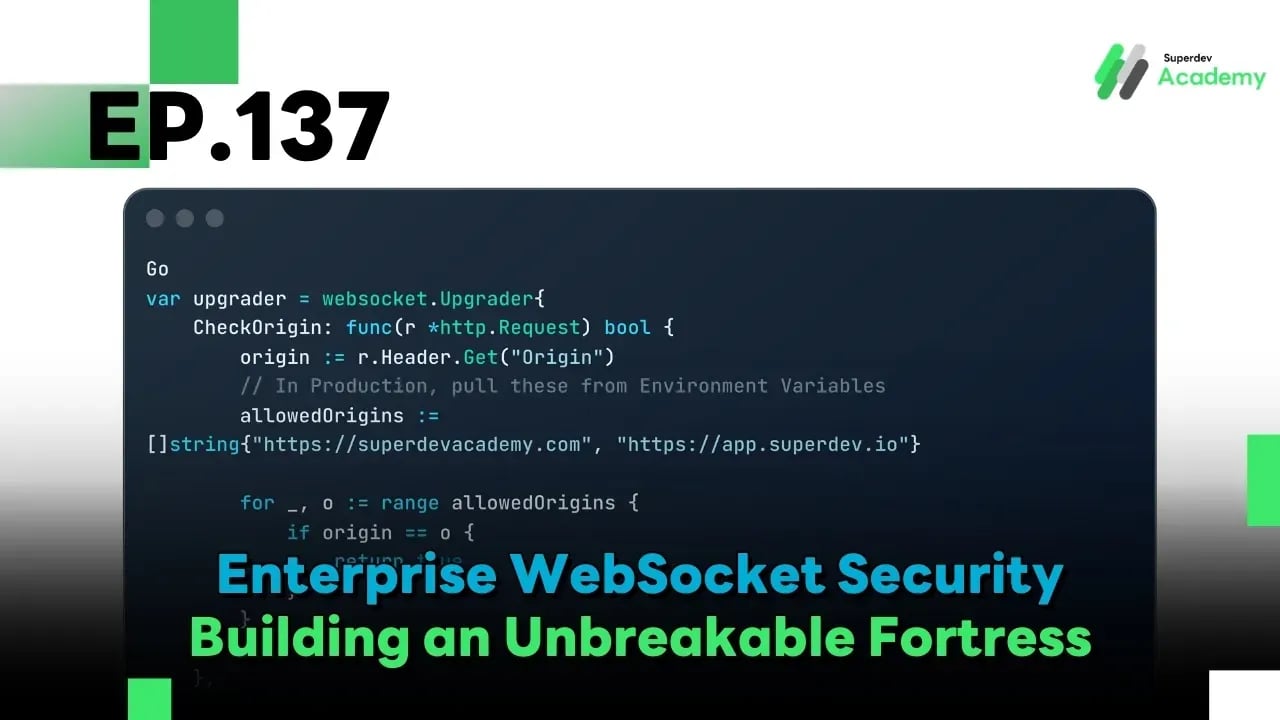
2. Origin Checking: Preventing CSWSH
Cross-Site WebSocket Hijacking (CSWSH) is a nightmare scenario. An attacker can trick a victim into visiting a malicious site that uses the victim's browser cookies to open a WebSocket connection to your server without their knowledge.
The Solution in Go:
Never set CheckOrigin to true in production! You must strictly whitelist allowed domains.
Go
var upgrader = websocket.Upgrader{
CheckOrigin: func(r *http.Request) bool {
origin := r.Header.Get("Origin")
// In Production, pull these from Environment Variables
allowedOrigins := []string{"https://superdevacademy.com", "https://app.superdev.io"}
for _, o := range allowedOrigins {
if origin == o {
return true
}
}
return false
},
}
3. Payload Validation & Size Limiting (Preventing OOM)
Malicious actors might send massive messages (e.g., a 100MB JSON) or deeply nested "recursive" JSON to cause Out of Memory (OOM) errors or CPU spikes on your server.
Best Practices:
- Hard Limit on Message Size: Use SetReadLimit to drop connections that exceed your size threshold immediately.
- Strict Schema Validation: Don't trust the data! Use Go structs with validation tags or JSON Schema to ensure the payload is clean and free of injection attempts.
Go
func (c *Client) readPump() {
// Limit chat messages to 4KB
c.conn.SetReadLimit(4096)
// Set a Read Deadline to prevent "Slowloris" style attacks
c.conn.SetReadDeadline(time.Now().Add(pongWait))
// ... logic follows
}
4. Rate Limiting & DoS Protection
WebSockets are Stateful. Maintaining 100,000 idle connections is far more resource-intensive than handling 100,000 stateless HTTP requests.
Protection Tactics:
- Connection Limits per User/IP: Limit a single User ID or IP to a reasonable number of concurrent connections (e.g., max 5) to prevent Connection Exhaustion.
- Distributed Rate Limiting: Use Redis to track active connection counts across multiple server instances (as discussed in EP.130).
- Aggressive Idle Timeouts: If a connection doesn't send data or respond to pings within a specific timeframe, close it to reclaim RAM.
5. Secure Infrastructure & Deep Defense
Security isn't just about code; it's about the environment where the code lives:
- TLS 1.3 & Strong Ciphers: Disable outdated protocols like TLS 1.0/1.1. Only allow secure cipher suites.
- Message-level Encryption: For ultra-sensitive data (like FinTech), encrypt the payload itself before sending it through the WebSocket to protect against SSL stripping.
- Non-Root Containers: Always run your Go app in Docker as a nonroot user. This limits the "blast radius" if an attacker manages to compromise the application.
- WAF (Web Application Firewall): Use a WAF that supports WebSocket Protocol Validation (like Cloudflare or AWS WAF) to filter out malformed packets at the edge.
Summary
Enterprise security isn't a "one-and-done" checklist; it's a Defense in Depth strategy. By vetting who gets in (Auth), inspecting what they bring (Payload), and protecting your space (Resource Management), you build a system that is truly resilient. Go's type-safety is a great start, but these best practices make your server an unbreakable fortress.
Next Episode (EP.138): We shift our focus from defense to Speed. We'll explore Monitoring Latency & Performance Optimization—how to shave off every millisecond and deliver a lag-free experience. Don't miss it!