25/04/2026 02:47am
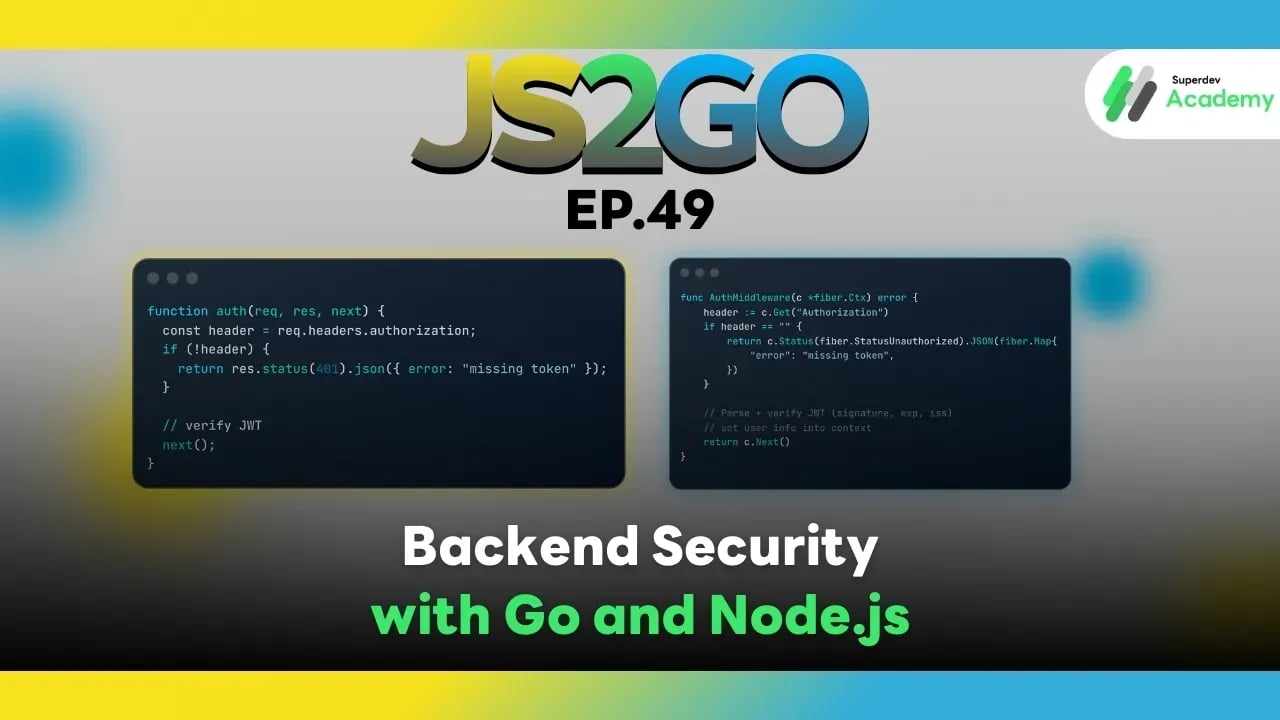
JS2GO EP.49 Backend Security with Go and Node.js
#authentication
#Authorization
#Secure API Design
#Backend
#Node.js
#Go
Building a Secure System from Day One
Not fixing issues after data leaks or security breaches
A good backend system is not judged only by how fast it is.
It must confidently answer these critical questions:
- Who is calling this API?
- Are they actually allowed to perform this action?
- Is the incoming data safe and trustworthy?
- Can the system withstand common attack vectors?
This article walks you through the core security fundamentals every production system must have — covering both Go and Node.js.
⭐ 1. Authentication vs Authorization (They Must Be Clearly Separated)
Many systems fail because these two concepts are mixed together.
| Concept | Meaning |
|---|---|
| Authentication (AuthN) | Who are you? |
| Authorization (AuthZ) | What are you allowed to do? |
Example:
- Login succeeds → Authentication passes
- Access to Admin page denied → Authorization fails
❗ Passing authentication does not mean full access.
These concerns must always be designed and implemented separately.
⭐ 2. Authentication Methods Used in Production
🔹 2.1 JWT (JSON Web Token)
Best suited for
- REST APIs
- Mobile applications
- Microservices
Characteristics
- Stateless
- Token sent with every request
- Easy to scale (no server-side session storage)
Flow
Login → JWT issued → Authorization: Bearer <token>
Go (Fiber) JWT Middleware (Correct Concept)
func AuthMiddleware(c *fiber.Ctx) error {
header := c.Get("Authorization")
if header == "" {
return c.Status(fiber.StatusUnauthorized).JSON(fiber.Map{
"error": "missing token",
})
}
// Parse and verify JWT (signature, exp, iss, aud)
// Set user info into context
return c.Next()
}
Node.js (Express)
function auth(req, res, next) {
const header = req.headers.authorization;
if (!header) {
return res.status(401).json({ error: "missing token" });
}
// verify JWT
next();
}
Important Notes
- Always validate
exp,iss, andaud - Never trust JWT payloads without verifying the signature
🔹 2.2 Session-based Authentication
Best suited for
- Web applications
- Server-rendered apps
Characteristics
- Stateful
- Session stored on the server
- Client uses cookies
Production requirements
HttpOnlySecureSameSite=StrictorLax
🔹 2.3 OAuth 2.0 / OpenID Connect
Best suited for
- Login with Google / GitHub
- Third-party integrations
Advantages
- No password storage in your system
- Reduced risk of credential leaks
⭐ 3. Authorization & RBAC (Role-Based Access Control)
RBAC controls permissions based on roles.
| Role | Permission |
|---|---|
| user | Read data |
| editor | Edit data |
| admin | Full access |
Go (Fiber)
func RequireRole(role string) fiber.Handler {
return func(c *fiber.Ctx) error {
if c.Locals("role") != role {
return c.Status(403).SendString("Forbidden")
}
return c.Next()
}
}
Node.js (Express)
function requireRole(role) {
return (req, res, next) => {
if (req.user.role !== role) {
return res.status(403).send("Forbidden");
}
next();
};
}
✔ Authentication = who
✔ Authorization = what they can do
Never merge these concerns into a single middleware.
⭐ 4. Input Validation The First Security Gate
❌ Never trust client input.
Unvalidated input can lead to:
- SQL Injection
- XSS
- Logic bugs
Go (Validator)
type CreateUserRequest struct {
Email string `validate:"required,email"`
Age int `validate:"gte=18"`
}
Use: go-playground/validator
Node.js (express-validator)
app.post(
"/user",
body("email").isEmail(),
body("age").isInt({ min: 18 }),
handler
);
⭐ 5. Preventing Common Attacks
🔥 5.1 SQL Injection
❌ Dangerous
SELECT * FROM users WHERE email = '${email}'
✅ Safe
- Prepared statements
- ORM / Query Builder
🔥 5.2 XSS (Cross-Site Scripting)
Mitigation:
- Escape output
- Never render untrusted HTML
- Use Content Security Policy (CSP)
🔥 5.3 CSRF
Mitigation:
- CSRF tokens
- SameSite cookies
- Validate Origin / Referer headers
⭐ 6. Security Best Practices (Production Checklist)
✔ Hash passwords using bcrypt or argon2
✔ Never log passwords or tokens
✔ HTTPS only
✔ Rate limiting (prevent brute-force attacks)
✔ Store secrets in environment variables
✔ Rotate tokens and secrets regularly
✔ Apply the Principle of Least Privilege
✔ Clearly separate roles
✔ Scan dependencies (npm audit, govulncheck)
⭐ 7. Overall Security Architecture
Client
→ Authentication
→ Authorization (RBAC)
→ Input Validation
→ Business Logic
→ Database
Good security is layered security — never rely on a single layer.
📌 Summary
Security is not an optional feature. It is the foundation of every production system.
If you design:
- Authentication correctly
- Authorization clearly
- Validation thoroughly
You will:
- Dramatically reduce risk
- Avoid emergency patching after attacks
- Build systems that survive long-term in production
🔵 Next Episode (Final): EP.50 Deploying Applications Go vs Node.js Production Guide
You will learn:
- Build and deployment strategies
- Docker and multi-stage builds
- Secrets and environment management
- CI/CD pipelines
- Zero-downtime deployment
- A full production deployment checklist 🚀